Tech Nuggets with Technology: This Blog provides you the content regarding the latest technology which includes gadjets,softwares,laptops,mobiles etc
Sunday, March 29, 2020
Retail Pooling: Online, offline firms share staff to deliver food, groceries
Covid-19 related searches grow multifold in two months: Report
Club Factory begins recruiting Indian e-commerce vendors to import essential goods
AR, VR and new-age tech companies gain ground amid Covid-19 outbreak
Sources: Facebook's security team had disinfo concerns about The Daily Wire's sites in 2019, clashing with the policy team, which prevented action being taken (New York Times)
New York Times:
Sources: Facebook's security team had disinfo concerns about The Daily Wire's sites in 2019, clashing with the policy team, which prevented action being taken — After spending billions to avoid a repeat of 2016, the tech giants are careening from crisis to crisis as their foes change tactics.
Zoho's lawsuit accuses rival Freshworks of stealing client data
Ecomm ops resume but deliveries may move in slow lane
Data from a whistleblower appears to show Saudi Arabia tracking the location of its citizens in the US by exploiting flaws in the SS7 phone network protocol (Stephanie Kirchgaessner/The Guardian)
Stephanie Kirchgaessner / The Guardian:
Data from a whistleblower appears to show Saudi Arabia tracking the location of its citizens in the US by exploiting flaws in the SS7 phone network protocol — Exclusive: Whistleblower's data suggests millions of tracking requests sent over four-month period
Smartphone makers ping Indian govt for essentials tag
Venezuela's mobile infrastructure, which was far from robust before the nation went into lockdown over COVID-19, is straining to handle surging internet traffic (Bloomberg)
Bloomberg:
Venezuela's mobile infrastructure, which was far from robust before the nation went into lockdown over COVID-19, is straining to handle surging internet traffic — - Data use has marked a new record every day during quarantine — Fuel shortages, tower vandalism strain neglected network
Elizabeth Warren for President open-sources its 2020 campaign tech
Democratic senator Elizabeth Warren may have ended her 2020 presidential run, but the tech used to drive her campaign will live on.
Members of her staff announced they would make public the top apps and digital tools developed in Warren’s bid to become the Democratic nominee for president.
“In our work, we leaned heavily on open source technology — and want to contribute back to that community…[by] open-sourcing some of the most important projects of the Elizabeth Warren campaign for anyone to use,” the Warren for President Tech Team said.
In a Medium post, members of the team — including chief technology strategist Mike Conlow and chief technology officer Nikki Sutton — previewed what would be available and why.
“Our hope is that other Democratic candidates and progressive causes will use the ideas and code we developed to run stronger campaigns and help Democrats win,” the post said.
Warren’s tech team listed several of the tools they’ve turned over to the open source universe via GitHub.
One of those tools, Spoke, is a peer to peer texting app, originally developed by MoveOn, which offered the Warren Campaign high volume messaging at a fraction of the costs of other vendor options. The team used it to send four million SMS messages on Super Tuesday alone.
Pollaris is a location lookup tool with an API developed to interface directly with Warren’s official campaign website and quickly direct supporters to their correct polling stations.
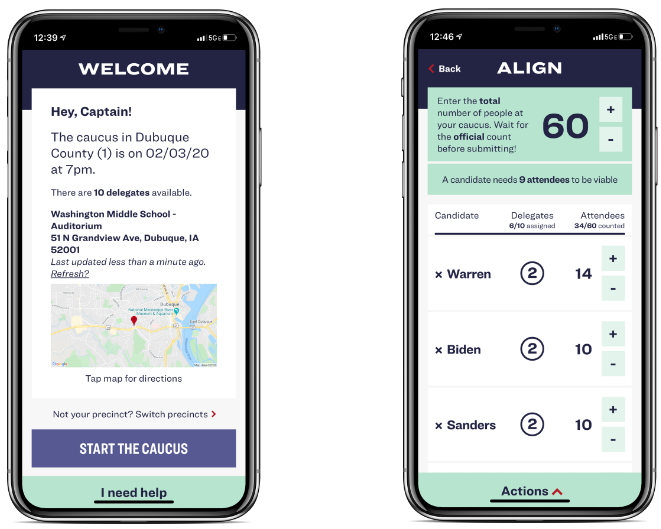
One of Elizabeth Warren’s presidential campaign app, Caucus, designed for calculating delegates. (Image: supplied)
Warren’s tech team will also open-source Switchboard (FE and BE) — which recruited and connected volunteers in primary states — and Caucus App, a delegate calculating and reporting tool.
The campaign’s Redhook tool took in web hook data in real time and experienced zero downtime.
“Our intention in open sourcing it is to demonstrate that some problems campaigns face do not require vendor tools and are solved…efficiently with a tiny bit of code,” said the Tech Team.
Elizabeth Warren ended her 2020 presidential bid on March 4 after failing to win a primary. Among her many policy proposals, the Massachusetts senator had proposed breaking up big tech companies, such as Google, Facebook and Amazon.
Her campaign will continue to share the tech tools they used on open source channels.
“We’ll have more to say in the coming weeks on all that we did with technology on our campaign,” the team said.
Test and trace with Apple and Google
After the shutdown, the testing and tracing. “Trace, test and treat is the mantra … no lockdowns, no roadblocks and no restriction on movement” in South Korea. “To suppress and control the epidemic, countries must isolate, test, treat and trace,” say WHO.
But what does “tracing” look like exactly? In Singapore, they use a “TraceTogether” app, which uses Bluetooth to track nearby phones (without location tracking), keeps local logs of those contacts, and only uploads them to the Ministry of Health when the user chooses/consents, presumably after a diagnosis, so those contacts can be alerted. Singapore plans to open-source the app.
In South Korea, the government texts people to let them know if they were in the vicinity of a diagnosed individual. The information conveyed can include the person’s age, gender, and detailed location history. Subsequently, even more details may be made available:
The level of detail provided by @Seoul_gov for each and every COVID-19 case in the city is astonishing:
Last name (which I've obscured)
Sex
Birth year
District of residence
Profession
Travel history
Contact with known cases
Hospital where they're being treated pic.twitter.com/GsI0QQPcVH— Victoria Kim (@vicjkim) March 24, 2020
In China, as you might expect, the surveillance is even more pervasive and draconian. Here, the pervasive apps Alipay and WeChat now include health codes – green, yellow, or red – set by the Chinese government, using opaque criteria. This health status is then used in hundreds of cities (and soon nationwide) to determine whether people are allowed to e.g. ride the subway, take a train, enter a building, or even exit a highway.
What about us, in the rich democratic world? Are we OK with the Chinese model? Of course not. The South Korean model? …Probably not. The Singaporean model? …Maybe. (I suspect it would fly in my homeland of Canada, for instance.) But the need to install a separate app, with TraceTogether or the directionally similar MIT project Safe Paths, is a problem. It works in a city-state like Singapore but will be much more problematic in a huge, politically divided nation like America. This will lead to inferior data blinded by both noncompliance and selection bias.
More generally, at what point does the urgent need for better data collide with the need to protect individual privacy and avoid enabling the tools for an aspiring, or existing, police state? And let’s not kid ourselves; the pandemic increases, rather than diminishes, the authoritarian threat.
Maybe, like the UK’s NHS, creators of new pandemic data infrastructures will promise “Once the public health emergency situation has ended, data will either be destroyed or returned” — but not all organizations instill the required level of trust in their populace. This tension has provoked heated discussion around whether we should create new surveillance systems to help mitigate and control the pandemic.
This surprises me greatly. Wherever you may be on that spectrum, there is no sense whatsoever in creating a new surveillance system — seeing as how multiple options already exist. We don’t like to think about it, much, but the cold fact is that two groups of entities already collectively have essentially unfettered access to all our proximity (and location) data, as and when they choose to do so.
I refer of course to the major cell providers, and to Apple & Google. This was vividly illustrated by data company Tectonix in a viral visualization of the spread of Spring Break partygoers:
Want to see the true potential impact of ignoring social distancing? Through a partnership with @xmodesocial, we analyzed secondary locations of anonymized mobile devices that were active at a single Ft. Lauderdale beach during spring break. This is where they went across the US: pic.twitter.com/3A3ePn9Vin
— Tectonix GEO (@TectonixGEO) March 25, 2020
Needless to say, Apple and Google, purveyors of the OSes on all those phones, have essentially the same capability as and when they choose to exercise it. An open letter from “technologists, epidemiologists & medical professionals” calls on “Apple, Google, and other mobile operating system vendors” (the notion that any other vendors are remotely relevant is adorable) “to provide an opt-in, privacy preserving OS feature to support contact tracing.”
They’re right. Android and iOS could, and should, add and roll out privacy-preserving, interoperable, TraceTogether-like functionality at the OS level (or Google Play Services level, to split fine technical hairs.) Granted, this means relying on corporate surveillance, which makes all of us feel uneasy. But at least it doesn’t mean creating a whole new surveillance infrastructure. Furthermore, Apple and Google, especially compared to cellular providers, have a strong institutional history and focus on protecting privacy and limiting the remit of their surveillance.
(Don’t believe me? Apple’s commitment to privacy has long been a competitive advantage. Google offers a thorough set of tools to let you control your data and privacy settings. I ask you: where is your cell service provider’s equivalent? Ah. Do you expect it to ever create one? I see. Would you also be interested in this fine, very lightly used Brooklyn Bridge I have on sale?)
Apple and Google are also much better suited to the task of preserving privacy by “anonymizing” data sets (I know, I know, but see below), or, better yet, preserving privacy via some form(s) of differential privacy and/or homomorphic encryption — or even some kind of zero-knowledge cryptography, he handwaved wildly. And, on a practical level, they’re more able than a third-party app developer to ensure a background service like that stays active.
Obviously this should all be well and firmly regulated. But at the same time, we should remain cognizant of the fact that not every nation believes in such regulation. Building privacy deep into a contact-tracing system, to the maximum extent consonant with its efficacy, is especially important when we consider its potential usage in authoritarian nations who might demand the raw data. “Anonymized” location datasets admittedly tend to be something of an oxymoron, but authoritarians may still be technically stymied by the difficulty of deanonymization; and if individual privacy can be preserved even more securely than that via some elegant encryption scheme, so much the better.
Compared to the other alternatives — government surveillance; the phone companies; or some new app, with all the concomitant friction and barriers to usage — Apple and Google are by some distance the least objectionable option. What’s more, in the face of this global pandemic they could roll out their part of the test-and-trace solution to three billion users relatively quickly. If we need a pervasive pandemic surveillance system, then let’s use one which (though we don’t like to talk about it) already exists, in the least dangerous, most privacy-preserving way.
Bihar Police 2020 – SI, Sergeant & Asst Superintendent Jail Mains Exam Date Postponed
Bihar Police SI Exam Date 2020 – SI, Sergeant & Asst Superintendent Jail Mains Exam Date Postponed
Technologists and healthcare workers team up for coronavirus response hackathon
A profile of Netflix co-CEO Greg Peters, who led the company's successful crackdown on password sharing and is now pushing a focus on live programming (Lucas Shaw/Bloomberg)
Lucas Shaw / Bloomberg : A profile of Netflix co-CEO Greg Peters, who led the company's successful crackdown on password sharing and ...
-
Jake Offenhartz / Gothamist : Since October, the NYPD has deployed a quadruped robot called Spot to a handful of crime scenes and hostage...
-
Andrew Tarantola / Engadget : An adapted excerpt from the book “Your Computer Is on Fire”, on how voice assistants like Siri and Alexa al...